How to find: Press “Ctrl + F” in the browser and fill in whatever wording is in the question to find that question/answer. If the question is not here, find it in Questions Bank.
NOTE: If you have the new question on this test, please comment Question and Multiple-Choice list in form below this article. We will update answers for you in the shortest time. Thank you! We truly value your contribution to the website.
CyberOps Associate (Version 1.0) – Modules 13 – 17: Threats and Attacks Group Exam
1. What is the significant characteristic of worm malware?
- Worm malware disguises itself as legitimate software.
- Once installed on a host system, a worm does not replicate itself.
- A worm must be triggered by an event on the host system.
- A worm can execute independently of the host system.
Explanation: Worm malware can execute and copy itself without being triggered by a host program. It is a significant network and Internet security threat.
2. What are the three major components of a worm attack? (Choose three.)
- a payload
- a propagation mechanism
- an infecting vulnerability
- a probing mechanism
- an enabling vulnerability
- a penetration mechanism
Explanation: A computer can have a worm installed through an email attachment, an executable program file, or a Trojan Horse. The worm attack not only affects one computer, but replicates to other computers. What the worm leaves behind is the payload–the code that results in some action.
3. A user is curious about how someone might know a computer has been infected with malware. What are two common malware behaviors? (Choose two.)
- The computer emits a hissing sound every time the pencil sharpener is used.
- The computer beeps once during the boot process.
- The computer gets increasingly slower to respond.
- No sound emits when an audio CD is played.
- The computer freezes and requires reboots.
Explanation: Common symptoms of computers infected with malware:
Appearance of files, applications, or desktop icons
Security tools such as antivirus software or firewalls turned off or changed
System crashes
Emails spontaneously sent to others
Modified or missing files
Slow system or browser response
Unfamiliar processes or services running
Unknown TCP or UDP ports open
Connections made to unknown remote devices
4. Which two types of attacks are examples of reconnaissance attacks? (Choose two.)
- brute force
- port scan
- ping sweep
- man-in-the-middle
- SYN flood
Explanation: Reconnaissance attacks attempt to gather information about the targets. Ping sweeps will indicate which hosts are up and responding to pings, whereas port scans will indicate on which TCP and UDP ports the target is listening for incoming connections. Man-in-the-middle and brute force attacks are both examples of access attacks, and a SYN flood is an example of a denial of service (DoS) attack.
5. An administrator discovers a vulnerability in the network. On analysis of the vulnerability the administrator decides the cost of managing the risk outweighs the cost of the risk itself. The risk is accepted, and no action is taken. What risk management strategy has been adopted?
- risk transfer
- risk acceptance
- risk reduction
- risk avoidance
Explanation: Risk acceptance is when the cost of risk management options outweighs the cost of the risk itself, the risk is accepted, and no action is taken.
6. Which protocol is exploited by cybercriminals who create malicious iFrames?
Explanation: An HTML element known as an inline frame or iFrame allows the browser to load a different web page from another source.
7. How can a DNS tunneling attack be mitigated?
- by preventing devices from using gratuitous ARP
- by using a filter that inspects DNS traffic
- by securing all domain owner accounts
- by using strong passwords and two-factor authentication
Explanation: To be able to stop DNS tunneling, a filter that inspects DNS traffic must be used. Also, DNS solutions such as Cisco OpenDNS block much of the DNS tunneling traffic by identifying suspicious domains.
8. What is the function of a gratuitous ARP sent by a networked device when it boots up?
- to request the netbios name of the connected system
- to request the MAC address of the DNS server
- to request the IP address of the connected network
- to advise connected devices of its MAC address
Explanation: A gratuitous ARP is often sent when a device first boots up to inform all other devices on the local network of the MAC address of the new device.
9. What is the result of a passive ARP poisoning attack?
- Data is modified in transit or malicious data is inserted in transit.
- Network clients experience a denial of service.
- Confidential information is stolen.
- Multiple subdomains are created.
Explanation: ARP poisoning attacks can be passive or active. The result of a passive attack is that cybercriminals steal confidential information. With an active attack, cybercriminals modify data in transit or they inject malicious data.
10. What are two methods used by cybercriminals to mask DNS attacks? (Choose two.)
- reflection
- shadowing
- domain generation algorithms
- fast flux
- tunneling
Explanation: Fast flux, double IP flux, and domain generation algorithms are used by cybercrimals to attack DNS servers and affect DNS services. Fast flux is a technique used to hide phishing and malware delivery sites behind a quickly-changing network of compromised DNS hosts (bots within botnets). The double IP flux technique rapidly changes the hostname to IP address mappings and the authoritative name server. Domain generation algorithms randomly generate domain names to be used as rendezvous points.
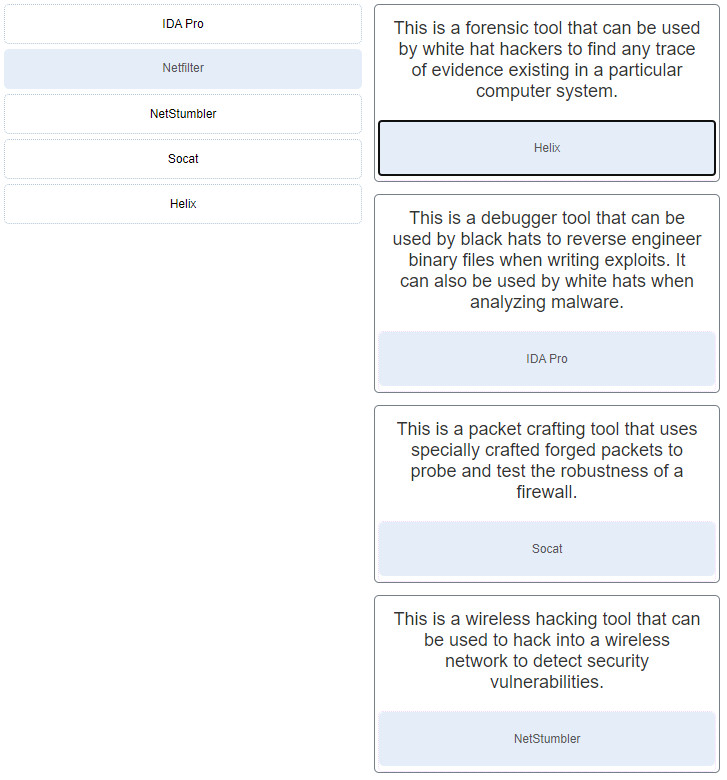
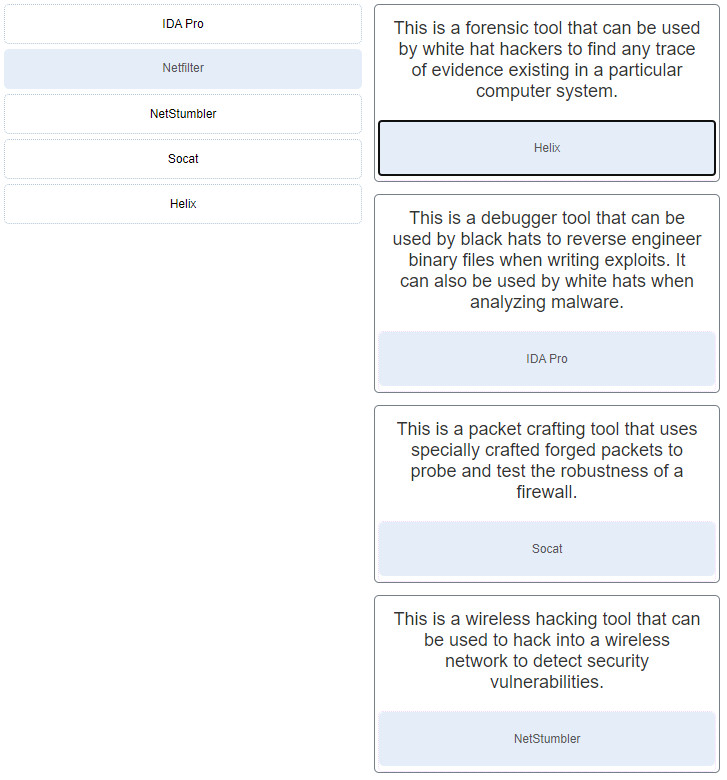
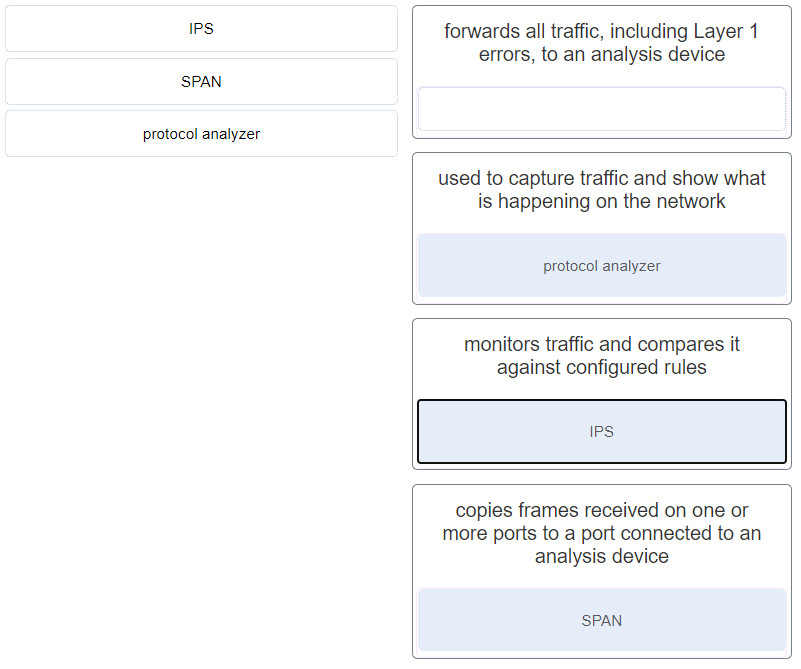
11. Match the security tool with the description. (Not all options apply.)
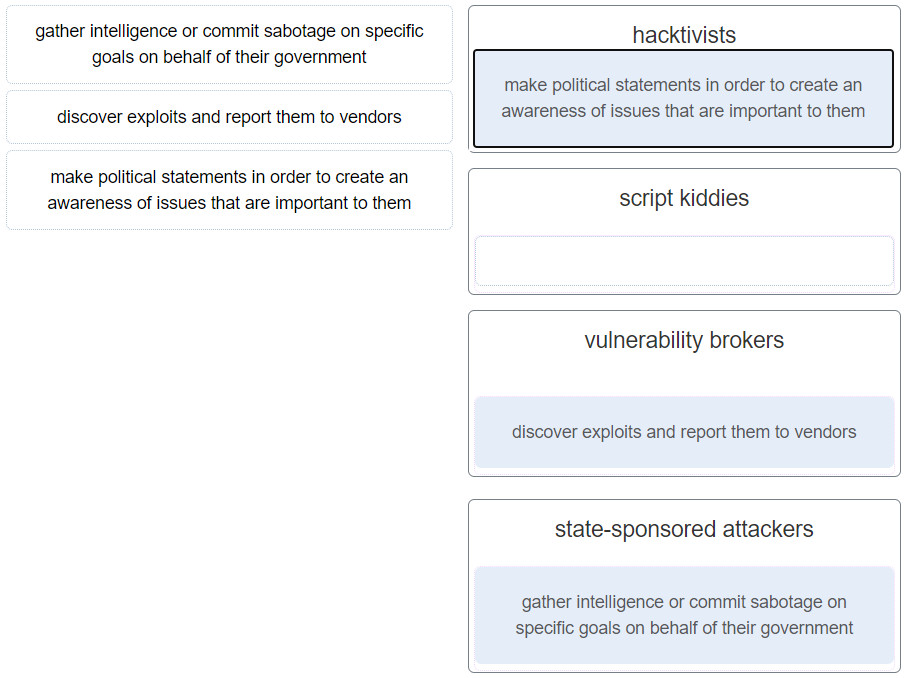
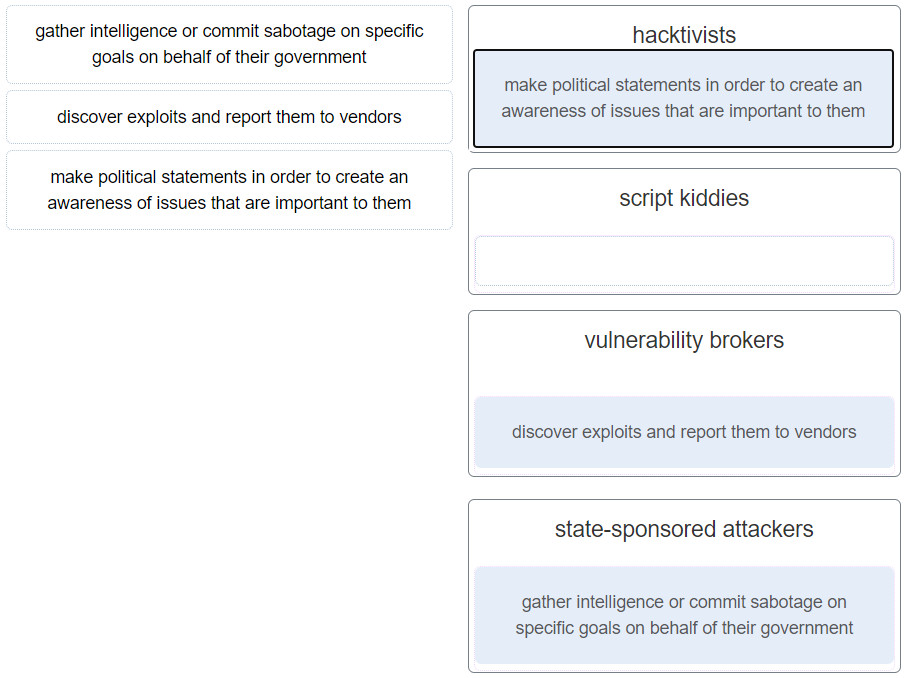
12. Match the type of cyberattackers to the description. (Not all options are used.)
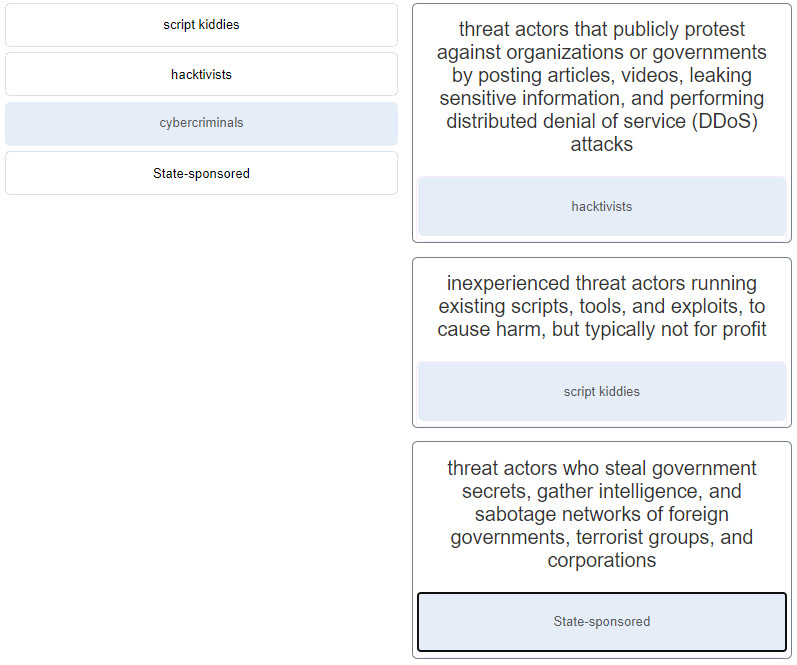
13. Match the threat actors with the descriptions. (Not all options are used.)
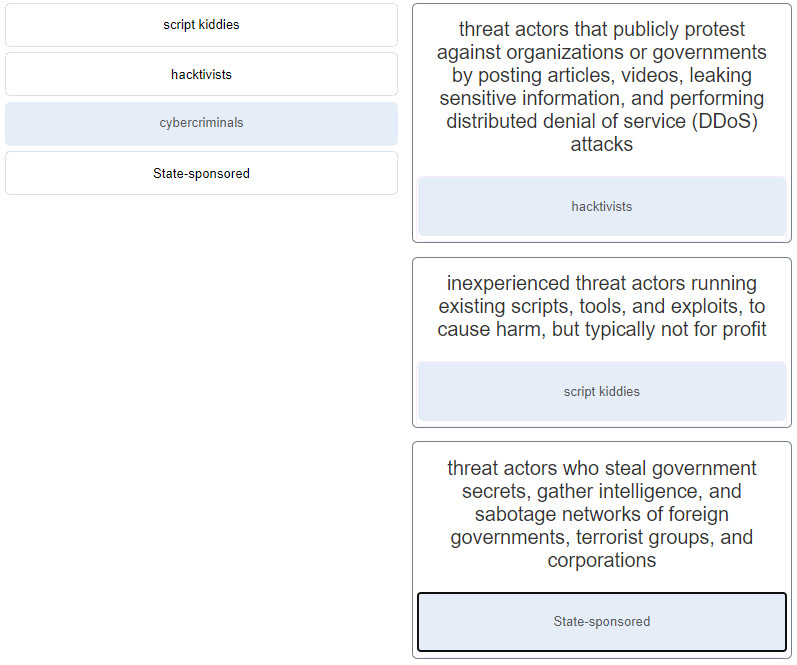
- hacktivists : threat actors that publicly protest against organizations or governments by posting articles, videos, leaking sensitive information, and performing distributed denial of service (DDoS) attacks
- script kiddies : inexperienced threat actors running existing scripts, tools, and exploits, to cause harm, but typically not for profit
- State-sponsored : threat actors who steal government secrets, gather intelligence, and sabotage networks of foreign governments, terrorist groups, and corporations
14. What scenario describes a vulnerability broker?
- a teenager running existing scripts, tools, and exploits, to cause harm, but typically not for profit
- a threat actor attempting to discover exploits and report them to vendors, sometimes for prizes or rewards
- a threat actor publicly protesting against governments by posting articles and leaking sensitive information
- a State-Sponsored threat actor who steals government secrets and sabotages networks of foreign governments
Explanation: Vulnerability brokers typically refers to grey hat hackers who attempt to discover exploits and report them to vendors, sometimes for prizes or rewards.
15. In what type of attack is a cybercriminal attempting to prevent legitimate users from accessing network services?
- DoS
- session hijacking
- MITM
- address spoofing
Explanation: In a DoS or denial-of-service attack, the goal of the attacker is to prevent legitimate users from accessing network services.
16. Which field in the IPv6 header points to optional network layer information that is carried in the IPv6 packet?
- traffic class
- version
- flow label
- next header
Explanation: Optional Layer 3 information about fragmentation, security, and mobility is carried inside of extension headers in an IPv6 packet. The next header field of the IPv6 header acts as a pointer to these optional extension headers if they are present.
17. Which type of attack is carried out by threat actors against a network to determine which IP addresses, protocols, and ports are allowed by ACLs?
- social engineering
- denial of service
- phishing
- reconnaissance
Explanation: Packet filtering ACLs use rules to filter incoming and outgoing traffic. These rules are defined by specifying IP addresses, port numbers, and protocols to be matched. Threat actors can use a reconnaissance attack involving port scanning or penetration testing to determine which IP addresses, protocols, and ports are allowed by ACLs.
18. What kind of ICMP message can be used by threat actors to create a man-in-the-middle attack?
- ICMP echo request
- ICMP unreachable
- ICMP redirects
- ICMP mask reply
Explanation:Common ICMP messages of interest to threat actors include the following:
ICMP echo request and echo reply: used to perform host verification and DoS attacks
ICMP unreachable: used to perform network reconnaissance and scanning attacks
ICMP mask reply: used to map an internal IP network
ICMP redirects: used to lure a target host into sending all traffic through a compromised device and create a man-in-the-middle attack
ICMP router discovery: used to inject bogus route entries into the routing table of a target host
19. What are two purposes of launching a reconnaissance attack on a network? (Choose two.)
- to escalate access privileges
- to prevent other users from accessing the system
- to scan for accessibility
- to gather information about the network and devices
- to retrieve and modify data
Explanation: Gathering information about a network and scanning for access is a reconnaissance attack. Preventing other users from accessing a system is a denial of service attack. Attempting to retrieve and modify data, and attempting to escalate access privileges are types of access attacks.
20. Which type of network attack involves randomly opening many Telnet requests to a router and results in a valid network administrator not being able to access the device?
- DNS poisoning
- man-in-the-middle
- SYN flooding
- spoofing
Explanation: The TCP SYN Flood attack exploits the TCP three-way handshake. The threat actor continually sends TCP SYN session request packets with a randomly spoofed source IP address to an intended target. The target device replies with a TCP SYN-ACK packet to the spoofed IP address and waits for a TCP ACK packet. Those responses never arrive. Eventually the target host is overwhelmed with half-open TCP connections and denies TCP services.
21. What functionality is provided by Cisco SPAN in a switched network?
- It mirrors traffic that passes through a switch port or VLAN to another port for traffic analysis.
- It prevents traffic on a LAN from being disrupted by a broadcast storm.
- It protects the switched network from receiving BPDUs on ports that should not be receiving them.
- It copies traffic that passes through a switch interface and sends the data directly to a syslog or SNMP server for analysis.
- It inspects voice protocols to ensure that SIP, SCCP, H.323, and MGCP requests conform to voice standards.
- It mitigates MAC address overflow attacks.
Explanation: SPAN is a Cisco technology used by network administrators to monitor suspicious traffic or to capture traffic to be analyzed.
22. Which statement describes an operational characteristic of NetFlow?
- NetFlow collects basic information about the packet flow, not the flow data itself.
- NetFlow captures the entire contents of a packet.
- NetFlow flow records can be viewed by the tcpdump tool.
- NetFlow can provide services for user access control.
Explanation: NetFlow does not capture the entire contents of a packet. Instead, NetFlow collects metadata, or data about the flow, not the flow data itself. NetFlow information can be viewed with tools such as nfdump and FlowViewer.
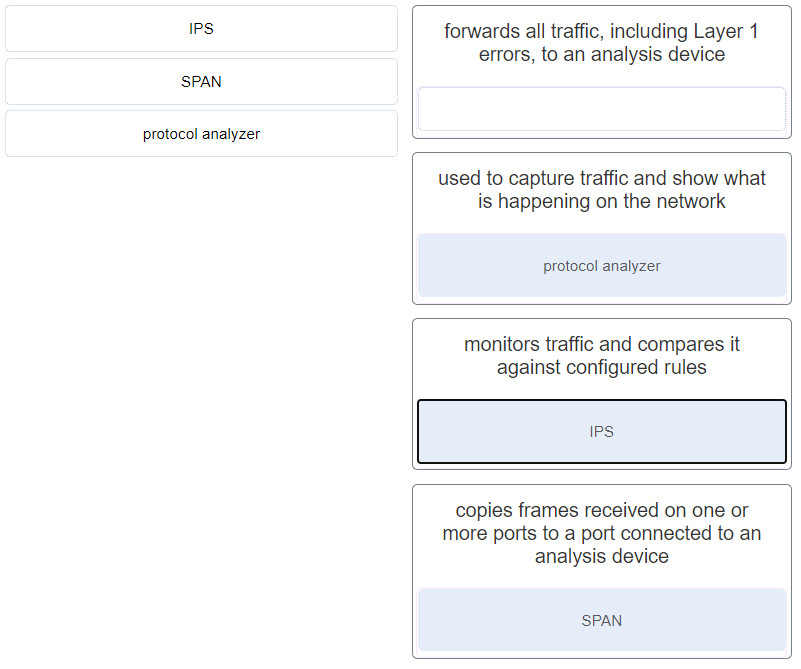
23.. Match the network monitoring solution with a description. (Not all options are used.)
24. Which technology is a proprietary SIEM system?
- StealthWatch
- NetFlow collector
- SNMP agent
- Splunk
Explanation: Security Information Event Management (SIEM) is a technology that is used in enterprise organizations to provide real-time reporting and long-term analysis of security events. Splunk is a proprietary SIEM system.
25. What are three functionalities provided by SOAR? (Choose three.)
- It automates complex incident response procedures and investigations.
- It provides 24×7 statistics on packets that flow through a Cisco router or multilayer switch.
- It uses artificial intelligence to detect incidents and aid in incident analysis and response.
- It presents the correlated and aggregated event data in real-time monitoring and long-term summaries.
- It provides a complete audit trail of basic information about every IP flow forwarded on a device.
- It provides case management tools that allow cybersecurity personnel to research and investigate incidents.
Explanation: SOAR security platforms offer these functionalities:
• Gather alarm data from each component of the system
• Provide tools that enable cases to be researched, assessed, and investigated
• Emphasize integration as a means of automating complex incident response workflows that enable more rapid response and adaptive defense strategies
• Include predefined playbooks that enable automatic response to specific threats
26. Which devices should be secured to mitigate against MAC address spoofing attacks?
- Layer 7 devices
- Layer 4 devices
- Layer 3 devices
- Layer 2 devices
Explanation: Layer 2 attacks such as MAC address spoofing can be mitigated by securing Layer 2 devices.
27. A network administrator is checking the system logs and notices unusual connectivity tests to multiple well-known ports on a server. What kind of potential network attack could this indicate?
- access
- denial of service
- information theft
- reconnaissance
Explanation: A reconnaissance attack is the unauthorized discovery and mapping of systems, services, or vulnerabilities. One of the most common reconnaissance attacks is performed by using utilities that automatically discover hosts on the networks and determine which ports are currently listening for connections.
28. What is a vulnerability that allows criminals to inject scripts into web pages viewed by users?
- Cross-site scripting
- XML injection
- buffer overflow
- SQL injection
Explanation: Cross-site scripting (XSS) allows criminals to inject scripts that contain malicious code into web applications.
29. Which cyber attack involves a coordinated attack from a botnet of zombie computers?
- ICMP redirect
- MITM
- DDoS
- address spoofing
Explanation: DDoS is a distributed denial-of-services attack. A DDoS attack is launched from multiple coordinated sources. The sources of the attack are zombie hosts that the cybercriminal has built into a botnet. When ready, the cybercriminal instructs the botnet of zombies to attack the chosen target.
30. What technique is a security attack that depletes the pool of IP addresses available for legitimate hosts?
- reconnaissance attack
- DHCP starvation
- DHCP spoofing
- DHCP snooping
Explanation: DHCP starvation attacks create a denial of service for network clients. The attacker sends DHCP discovery messages that contain fake MAC addresses in an attempt to lease all of the IP addresses. In contrast, DHCP spoofing occurs when a cybercriminal configures a rogue DHCP server to provide network clients with incorrect IP configuration information.
31 Which type of Trojan horse security breach uses the computer of the victim as the source device to launch other attacks?
Explanation: The attacker uses a proxy Trojan horse attack to penetrate one device and then use that device to launch attacks on other devices. The Dos Trojan horse slows or halts network traffic. The FTP trojan horse enables unauthorized file transfer services when port 21 has been compromised. A data-sending Trojan horse transmits data back to the hacker that could include passwords.
32. What are two examples of DoS attacks? (Choose two.)
- buffer overflow
- SQL injection
- port scanning
- phishing
- ping of death
Explanation: The buffer overflow and ping of death DoS attacks exploit system memory-related flaws on a server by sending an unexpected amount of data or malformed data to the server.
33. Why would a rootkit be used by a hacker?
- to try to guess a password
- to reverse engineer binary files
- to gain access to a device without being detected
- to do reconnaissance
Explanation: Hackers use rootkits to avoid detection as well as hide any software installed by the hacker.
34. What causes a buffer overflow?
- sending too much information to two or more interfaces of the same device, thereby causing dropped packets
- attempting to write more data to a memory location than that location can hold
- sending repeated connections such as Telnet to a particular device, thus denying other data sources
- downloading and installing too many software updates at one time
- launching a security countermeasure to mitigate a Trojan horse
Explanation: By sending too much data to a specific area of memory, adjacent memory locations are overwritten, which causes a security issue because the program in the overwritten memory location is affected.
35. Which type of security threat would be responsible if a spreadsheet add-on disables the local software firewall?
- DoS
- Trojan horse
- buffer overflow
- brute-force attack
Explanation: A Trojan horse is software that does something harmful, but is hidden in legitimate software code. A denial of service (DoS) attack results in interruption of network services to users, network devices, or applications. A brute-force attack commonly involves trying to access a network device. A buffer overflow occurs when a program attempts to store more data in a memory location than it can hold.
36. Which two types of hackers are typically classified as grey hat hackers? (Choose two.)
- hacktivists
- cyber criminals
- vulnerability brokers
- script kiddies
- state-sponsored hackers
Explanation: Grey hat hackers may do unethical or illegal things, but not for personal gain or to cause damage. Hacktivists use their hacking as a form of political or social protest, and vulnerability brokers hack to uncover weaknesses and report them to vendors. Depending on the perspective one possesses, state-sponsored hackers are either white hat or black hat operators. Script kiddies create hacking scripts to cause damage or disruption. Cyber criminals use hacking to obtain financial gain by illegal means.
37. A white hat hacker is using a security tool called Skipfish to discover the vulnerabilities of a computer system. What type of tool is this?
- debugger
- fuzzer
- vulnerability scanner
- packet sniffer
Explanation: Fuzzers are tools used by threat actors when attempting to discover the vulnerabilities of a computer system. Examples of fuzzers include Skipfish, Wapiti, and W3af.
38. Which two functions are provided by NetFlow? (Choose two.)
- It uses artificial intelligence to detect incidents and aid in incident analysis and response.
- It provides a complete audit trail of basic information about every IP flow forwarded on a device.
- It provides 24×7 statistics on packets that flow through a Cisco router or multilayer switch.
- It allows an administrator to capture real-time network traffic and analyze the entire contents of packets.
- It presents correlated and aggregated event data in real-time monitoring and long-term summaries.
Explanation: NetFlow is a Cisco IOS technology that provides statistics and complete audit trails on TCP/IP flows on the network. Some of the capabilities of NetFlow include the following: 24×7 network and security monitoring, network planning, traffic analysis, identification of network bottlenecks, and IP accounting for billing purposes.
39. Which statement describes the function of the SPAN tool used in a Cisco switch?
- It is a secure channel for a switch to send logging to a syslog server.
- It provides interconnection between VLANs over multiple switches.
- It supports the SNMP trap operation on a switch.
- It copies the traffic from one switch port and sends it to another switch port that is connected to a monitoring device.
Explanation: To analyze network traffic passing through a switch, switched port analyzer (SPAN) can be used. SPAN can send a copy of traffic from one port to another port on the same switch where a network analyzer or monitoring device is connected. SPAN is not required for syslog or SNMP. SPAN is used to mirror traffic, while syslog and SNMP are configured to send data directly to the appropriate server.
40. What are two evasion methods used by hackers? (Choose two.)
- scanning
- access attack
- resource exhaustion
- phishing
- encryption
Explanation: The following methods are used by hackers to avoid detection:Encryption and tunneling – hide or scramble the malware content
Resource exhaustion – keep the host device too busy to detect the invasion
Traffic fragmentation – split the malware into multiple packets
Protocol-level misinterpretation – sneak by the firewall
Pivot – use a compromised network device to attempt access to another device
Rootkit – allow the hacker to avoid detection as well as hide software installed by the hacker
41. Which attack involves threat actors positioning themselves between a source and destination with the intent of transparently monitoring, capturing, and controlling the communication?
- man-in-the-middle attack
- DoS attack
- ICMP attack
- SYN flood attack
Explanation: The man-in-the-middle attack is a common IP-related attack where threat actors position themselves between a source and destination to transparently monitor, capture, and control the communication.
42. What is the goal of a white hat hacker?
- validating data
- modifying data
- stealing data
- protecting data
Explanation: White hat hackers are actually “good guys” and are paid by companies and governments to test for security vulnerabilities so that data is better protected.
43. Once a cyber threat has been verified, the US Cybersecurity Infrastructure and Security Agency (CISA) automatically shares the cybersecurity information with public and private organizations. What is this automated system called?
Explanation: Governments are now actively promoting cybersecurity. For instance, the US Cybersecurity Infrastructure and Security Agency (CISA) is leading efforts to automate the sharing of cybersecurity information with public and private organizations at no cost. CISA use a system called Automated Indicator Sharing (AIS). AIS enables the sharing of attack indicators between the US government and the private sector as soon as threats are verified. CISA offers many resources that help to limit the size of the United States attack surface.
44. A user receives a phone call from a person who claims to represent IT services and then asks that user for confirmation of username and password for auditing purposes. Which security threat does this phone call represent?
- spam
- anonymous keylogging
- DDoS
- social engineering
Explanation: Social engineering attempts to gain the confidence of an employee and convince that person to divulge confidential and sensitive information, such as usernames and passwords. DDoS attacks, spam, and keylogging are all examples of software based security threats, not social engineering.
45. Which two characteristics describe a worm? (Choose two)
- is self-replicating
- travels to new computers without any intervention or knowledge of the user
- infects computers by attaching to software code
- hides in a dormant state until needed by an attacker
- executes when software is run on a computer
Explanation: Worms are self-replicating pieces of software that consume bandwidth on a network as they propagate from system to system. They do not require a host application, unlike a virus. Viruses, on the other hand, carry executable malicious code which harms the target machine on which they reside.
46. An attacker is redirecting traffic to a false default gateway in an attempt to intercept the data traffic of a switched network. What type of attack could achieve this?
- MAC address snoopin
- DHCP snooping
- MAC address starvation
- DHCP spoofing
Explanation: In DHCP spoofing attacks, an attacker configures a fake DHCP server on the network to issue DHCP addresses to clients with the aim of forcing the clients to use a false default gateway, and other false services. DHCP snooping is a Cisco switch feature that can mitigate DHCP attacks. MAC address starvation and MAC address snooping are not recognized security attacks. MAC address spoofing is a network security threat.
47. What would be the target of an SQL injection attack?
Explanation: SQL is the language used to query a relational database. Cybercriminals use SQL injections to get information, create fake or malicious queries, or to breach the database in some other way.
48. The IT department is reporting that a company web server is receiving an abnormally high number of web page requests from different locations simultaneously. Which type of security attack is occurring?
- social engineering
- adware
- DDoS
- phishing
- spyware
Explanation: Phishing, spyware, and social engineering are security attacks that collect network and user information. Adware consists, typically, of annoying popup windows. Unlike a DDoS attack, none of these attacks generate large amounts of data traffic that can restrict access to network services.
49. Why would an attacker want to spoof a MAC address?
- so that the attacker can capture traffic from multiple VLANs rather than from just the VLAN that is assigned to the port to which the attacker device is attached
- so that a switch on the LAN will start forwarding frames to the attacker instead of to the legitimate host
- so that a switch on the LAN will start forwarding all frames toward the device that is under control of the attacker (that can then capture the LAN traffic)
- so that the attacker can launch another type of attack in order to gain access to the switch
Explanation: MAC address spoofing is used to bypass security measures by allowing an attacker to impersonate a legitimate host device, usually for the purpose of collecting network traffic.
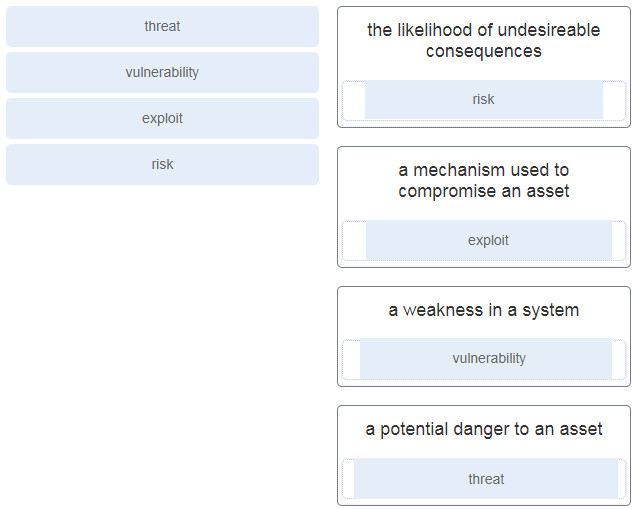
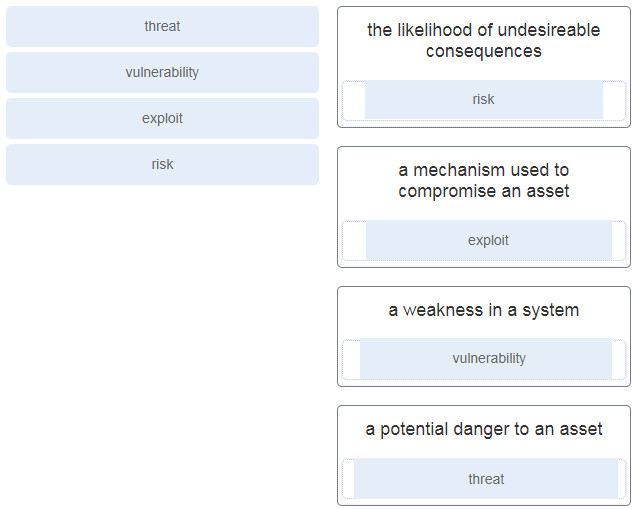
50. Match the security concept to the description.
51. Which two characteristics describe a virus? (Choose two.)
- Malicious code that can remain dormant before executing an unwanted action.
- Malware that executes arbitrary code and installs copies of itself in memory.
- Malware that relies on the action of a user or a program to activate.
- Program code specifically designed to corrupt memory in network devices.
- A self-replicating attack that is independently launched.
Explanation: A virus is malicious code that is attached to legitimate programs or executable files. Most viruses require end user activation, can lie dormant for an extended period, and then activate at a specific time or date. In contrast, a worm executes arbitrary code and installs copies of itself in the memory of the infected computer. The main purpose of a worm is automatic replication to spread quickly across a network. A worm does not require a host program to run.
52. Which type of security attack would attempt a buffer overflow?
- ransomware
- reconnaissance
- DoS
- scareware
Explanation: Denial of service (DoS) attacks attempt to disrupt service on the network by either sending a particular device an overwhelming amount of data so no other devices can access the attacked device or by sending malformed packets.







Dumps for the https://www.valid4sure.com/AZ-204-exam-answers.html are collections of sample questions and solutions produced by people or businesses to aid candidates in getting ready for the real test. These practice tests are made to help applicants figure out where they need to improve by simulating the real exam. The AZ-204 exam questions are broken up into several sections that cover various subjects, including Azure App Service, Azure Functions, Azure Storage, and others.
ReplyDelete